From 2018 to 2024, I conducted research on developing tools and techniques for the automated discovery of vulnerabilities in cryptographic implementations. Although cryptographic algorithms may be mathematically secure, their physical execution on diverse hardware introduces environmental variables that can compromise safety. My work centered on analyzing exposure to side-channel leaks such as timing, cache and microarchitectural side channels, and power consumption, which significantly complicate the resilience of cryptographic products against key and data exposure.
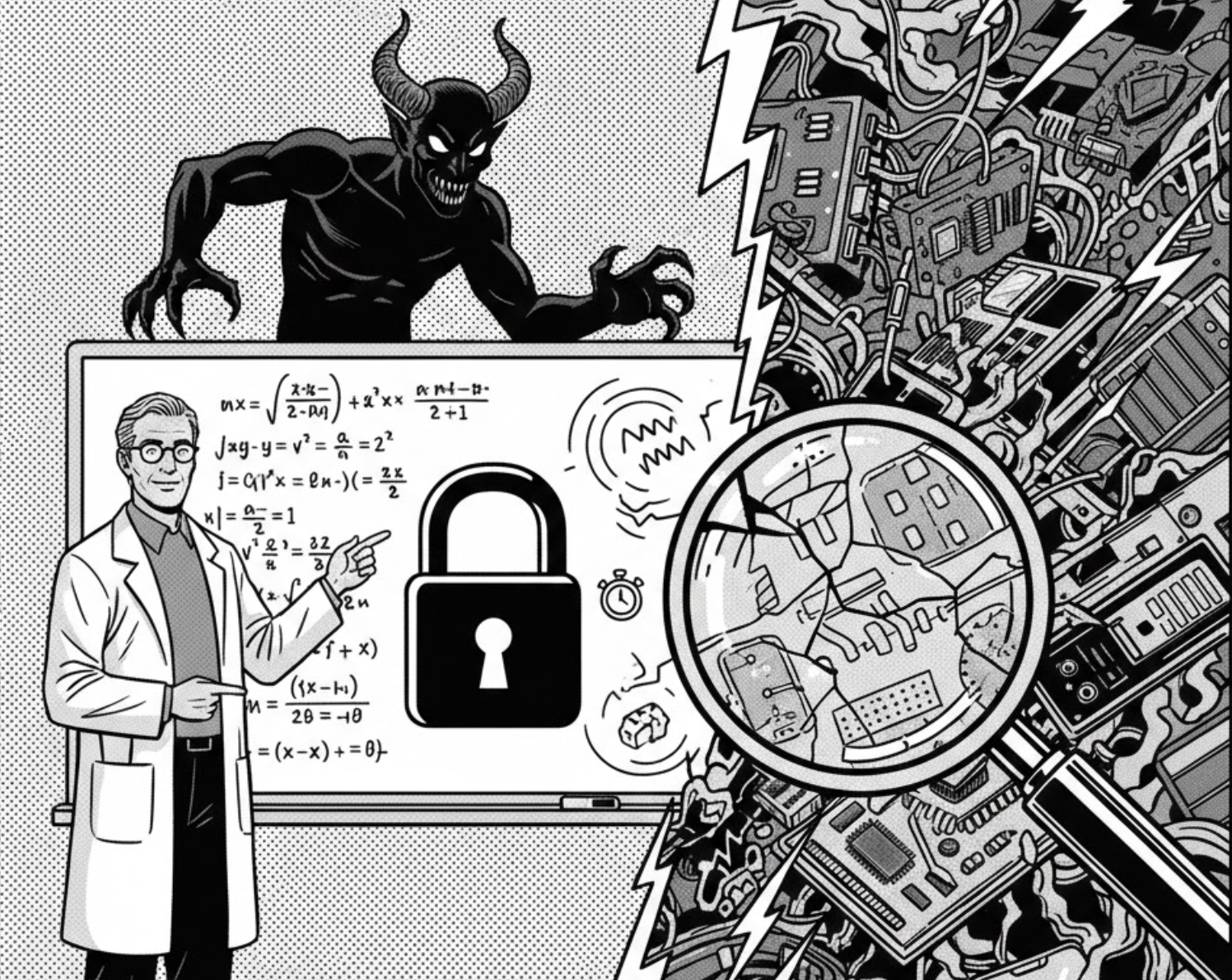
My research led to the discovery of critical vulnerabilities in widely deployed systems. In MemJam, I demonstrated that software-level assumptions about cache timing are undermined by microarchitectures leaking intra-cache granular data, allowing for key recovery against Intel IPP’s constant-time protections. Additionally, in TPM-Fail, I identified remote timing vulnerabilities in highly vetted TPM firmware, proving that subtle execution variations can lead to full signing and attestation key recovery.
Manual analysis of cryptographic systems is increasingly unsustainable as developers consistently reintroduce vulnerabilities across product generations. To address this, we developed MicroWalk, a dynamic binary analysis framework combining binary instrumentation, fuzzing, and mutual information (MI) analysis, which uncovered further vulnerabilities in the Intel IPP library. At Google, I contributed to GPAM, a transformer-based ML pipeline for detecting secret key leakage via power and electromagnetic signals. Furthermore, with DroidCCT, we established the first comprehensive distributed compliance framework to automatically detect cryptographic gaps across the software, firmware, and hardware of Android devices.
These efforts have led to the remediation of several vulnerabilities in highly trusted systems and sparked further research and development. Collaborators, since, have extended MicroWalk-CI to discover additional vulnerabilities in software cryptography. And, Google is actively extending and applying GPAM as an open-source Side-channel Analysis ML (SCAAML) model to evaluate new hardware countermeasures.